Ancient Origins
Steganography has roots stretching back thousands of years. Long before the digital age, ancient civilizations devised ingenious methods to transmit secret messages under the noses of adversaries and authorities.
✂️ Histiaeus and the Shaved Head (c. 500 BCE):One of the earliest documented examples comes from ancient Greece. Histiaeus, a Greek ruler and advisor to the Persian king Darius, needed to send a covert message to his ally Aristagoras to incite a rebellion. Knowing that written correspondence could be intercepted, Histiaeus employed a creative tactic: he shaved the head of a trusted slave, tattooed the secret message onto the exposed scalp, and waited for the hair to regrow. Once the slave's hair had fully covered the message, he was sent to Aristagoras. Upon arrival, the recipient shaved the slave's head to uncover the hidden tattoo, a method that was simple, low-tech, and effective against conventional surveillance.

Stone carving
🕯️ Demaratus and Wax Tablets: Another Greek figure, Demaratus, used steganography to warn Sparta about an impending Persian invasion. He wrote the message on a wooden tablet and then covered the writing with a layer of wax, creating the appearance of a blank, unused tablet. This technique exploited the assumption that only visible ink or carving would carry meaning. The recipient, upon being alerted, scraped away the wax to reveal the hidden message. This method demonstrates an early use of camouflage by material layering, a principle still echoed in digital steganography today.

Wax tablet
💌 Covert Messaging in Ancient China: Ancient Chinese practices also reveal a sophisticated understanding of information concealment. In some cases, sensitive messages were inscribed on fine silk or paper, which was then tightly rolled into small pellets and sealed with wax. Couriers would swallow these pellets or hide them in bodily cavities, ensuring that the information could pass undetected through hostile territory or checkpoints. This form of biological concealment highlights a distinctly human element in early steganography—where the messenger's body itself became the medium of storage.
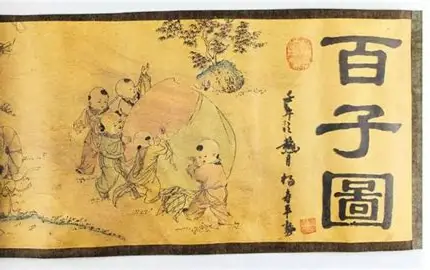
Ancient silk paper
Medieval and Renaissance
As the centuries progressed, the art of steganography evolved alongside advancements in writing, encryption, and communication technology. During the Middle Ages, secrecy was paramount for both political leaders and religious figures, especially in the context of espionage and warfare. However, the reliance on written manuscripts also meant that new methods of hidden communication became more creative and complex.
🔐 Medieval Cryptography and Secret Writing: In the Middle Ages, cryptography (the art of encoding information) often went hand in hand with steganography. As monarchs, church leaders, and military commanders needed secure communication, they turned to cryptic writing systems. One famous example is Albertus Magnus, a 13th-century scholar who wrote extensively on the use of ciphers to disguise secret messages. Although not technically steganography, his work in encryption laid the groundwork for future developments in concealed communication. Invisible ink also gained popularity in this period, especially during the Renaissance, as it allowed messages to be hidden and revealed only under certain conditions, such as by heat or chemical reaction. This technique, using substances like lemon juice or milk, is considered an early form of chemical steganography.
📜 Johannes Trithemius's Steganographia: In 1499, Trithemius authored Steganographia, a treatise that combined cryptography and steganography, disguised as a book on magic. This work introduced methods of hiding messages within texts and was influential in the development of cryptographic techniques.
🎨 Renaissance Advances in Steganography: The Renaissance period (14th to 17th centuries) saw the rise of more sophisticated methods of information concealment, as scholars and inventors turned their attention to the possibilities of hidden communication. One notable figure is Giambattista della Porta, an Italian polymath who published treatises on the use of invisible ink in the 16th century. His work demonstrated a growing awareness of how secret messages could be transmitted without raising suspicion.
During this time, symbolic communication also flourished. In espionage, coded languages and pictorial symbols became common, allowing agents to hide messages within seemingly innocuous writings or artwork. For example, artists often incorporated hidden symbols or messages within their paintings to communicate with secret societies or convey political dissent in ways that could evade censors.
Digital Age
💾 1980s: With the advent of computers, steganography entered the digital realm. From the 1980s onward, the rise of personal computers and digital media enabled new forms of steganography, allowing information to be embedded within images, audio files, and even video. This marked a significant evolution from traditional methods, leveraging binary data to conceal messages in a way that was far less detectable to the human senses.
🌐 1990s: The growing accessibility of the internet and multimedia files in the 1990s brought digital steganography into wider use. Academic and hobbyist interest surged, and researchers began developing specialized tools for hiding data in image formats like BMP and JPEG. This period also saw the emergence of steganalysis, the science of detecting steganography, as a countermeasure, particularly within information security circles.
💻 2000s: As digital communication and file-sharing exploded, steganography became more sophisticated and, in some cases, weaponized. Steganographic techniques were increasingly used for both legitimate privacy protection and malicious purposes, such as covert communication by cybercriminals. Security experts began to view steganography as a double-edged sword, a powerful tool for both protecting data and hiding threats.
📱 2010s-Present: Modern steganography has evolved alongside advances in computing, cybersecurity, and artificial intelligence. Today, information can be concealed not just in static media files, but also in streaming data, network protocols, and even within the structure of machine learning models. Tools have become more user-friendly and accessible, while methods more complex and difficult to detect. In cybersecurity, steganography is both a protective measure for privacy and intellectual property, and a threat vector used by malware to exfiltrate data or coordinate attacks without detection.